
Keep your iPhone text messages private with these tips
If you’re a business owner who relies on text messages to communicate with employees, clients, or customers, it’s essential to ensure the privacy and security


If you’re a business owner who relies on text messages to communicate with employees, clients, or customers, it’s essential to ensure the privacy and security
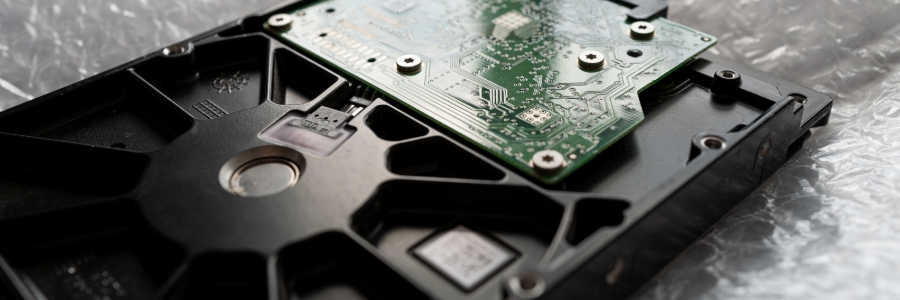
Solid-state drives (SSDs) are fast becoming the standard for data storage because of their many advantages over hard disk drives (HDDs). Here are the top

Many iPad users are usually happy with their device, but there are a few who want to install apps that are not on the App

Keyboard shortcuts can enhance users’ productivity and save time, but not everyone knows about them. If you own a Mac, these are the keyboard shortcuts

Employees rely on smartphones to contact clients and coworkers as well as to work on the go. So if your iPhone runs out of battery,

Whether you purchased an iPad for personal use or work, there are several things you need to configure before using it. But if you’re not

Cybersecurity experts Rob Wright (Dark Reading), David Jones (Cybersecurity Dive), and Alissa Irei (TechTarget Search Security) recently came together to discuss the future of online

Cloud computing is the use of remote servers to store, manage, and process data, freeing businesses from the limits of physical infrastructure. For small businesses,

Your bathroom, your kitchen table, even your dreams — if it’s part of your life, health tech wants in. CES 2026, the world’s biggest technology

Strong passwords are one of the easiest and most effective ways to protect online accounts. Still, many businesses use weak or reuse credentials. Learning how

Collaboration should be easy, not a chore. That’s why Microsoft Loop is such a game changer for teams of all sizes. It’s a simple way

Cybersecurity is no longer just a concern for big corporations. In this article, we explore how cloud technology helps smaller businesses tap into enterprise-grade security,